Cyber attacks are constant and evolving. Zapata Technology takes a proactive, offense-informed approach to cybersecurity — identifying and eliminating vulnerabilities before adversaries can exploit them. Our TS/SCI cleared cybersecurity engineers bring real-world defense experience to every engagement.
Preemptive Cybersecurity Services
We assume every network has been compromised. Our preemptive services validate your security posture, identify gaps, and provide actionable remediation — aligned with DoD Zero Trust mandates and NIST frameworks.
Network, application, wireless, and social engineering testing. We simulate real-world adversary tactics to identify exploitable vulnerabilities in classified and unclassified environments.
Comprehensive scanning, analysis, and prioritized remediation planning. Continuous vulnerability management aligned with DISA STIGs and NIST 800-53 controls.
Adversarial simulation and defensive response exercises that test your organization’s detection, response, and recovery capabilities under realistic attack scenarios.
Assessment of network architecture, segmentation, access controls, and data flows against Zero Trust principles and DoD reference architectures.
CMMC, NIST 800-171, RMF, and FISMA readiness assessments. We identify compliance gaps and build actionable Plans of Action and Milestones (POA&M).
Development of incident response plans, playbooks, and tabletop exercises. We prepare your team to detect, contain, and recover from security incidents rapidly.
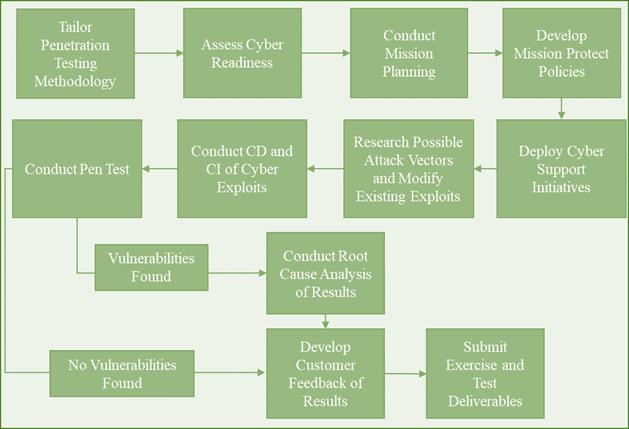
Our Methodology
We follow NIST SP 800-115 and PTES guidelines, ensuring systematic and thorough coverage across all assessment phases.
Define objectives, rules of engagement, and scope boundaries
OSINT gathering, network mapping, and attack surface enumeration
Automated and manual vulnerability identification and validation
Controlled exploitation to validate vulnerabilities and assess impact
Detailed findings, risk ratings, and prioritized remediation guidance
Why Zapata Technology
Our cybersecurity engineers hold active Top Secret/SCI clearances, enabling testing on the most sensitive classified networks.
Every engagement follows our CMMI Level 3 certified processes, ensuring repeatable, measurable, and auditable results.
Prime contractor on Marines MCTSSA cybersecurity programs. Direct support to DISA/JITC for security testing and evaluation.
Ready to Assess Your Security Posture?
Contact our cybersecurity team to discuss penetration testing, vulnerability assessments, or compliance readiness for your defense programs.
